What is facial recognition technology?
Essentially, a facial recognition technology is used to verify and identify a person’s features on a video source from a digital image or a video frame. There are several approaches to the working of a facial recognition system, but generally, the algorithm compares different facial features as against an image encompassed within a database. Classified as Biometric Artificial Intelligence, the application can distinctively recognize a face by analyzing patterns depending upon facial shapes and textures.
FRT or Facial Recognition Technology has found wider usage in robotics, on mobile platforms and similar areas. Predominantly a computer application, FRT can be used in access control parallel to other biometric systems such as iris and fingerprint recognition. Facial recognition is an accepted tool and is popular in commercial surveillance, video database, automatic indexing of images and much more.
In the early 2000s, face detection became mainstream when Paul Viola and Michael Jones incorporated a fast means of detecting appearances on cheap cameras. Today, the technology has evolved beyond imagination to provide reliable face detection solutions.
Facial Recognition Software
XCEL Corp is a leading provider of Facial Recognition Software systems that are capable of verifying and analyzing the patterns of a person’s facial contours. Mostly used for security reasons, this is a progressive area and has enough potential especially when related to law enforcement although other enterprises are slowly adopting the technology to manage in-house, on-premise and other kinds of threats. While used predominantly for safety purposes the software holds ground even when smart analytics are required.
Biometric Identification
Historically, there have been several other forms of biometric identification systems such as fingerprint, voice, etc., where a computer analyzes this piece of data with a specific set of markers. Conceptually analogous to the lines of fingerprint identification and any other forms of biometric comparison, the programming is different in terms where it finds a critical threshold similarity between the sample and the existing database after which a match is declared.
Software, Algorithms, and Approaches
FRT uses software and algorithms to accentuate relevant details of an image and accomplish facial identification. There are several methods of approach and strategies adopted for the process. However, for an ideal system, true positives and false positives both have to be very high and very low, respectively.
Knowledge-based
This method calculates facial parameters such as mouth, nose, eyes, lips and their relative intensity. To achieve accurate verification, false detection is reduced. This technique is absolutely ideal when identifying face images from the front.
Feature-based
- The approach is basically divided into three parts, Low-level Analysis, Feature Analysis, and Active-Shape Model. The properties of pixels are used to segment visual features in Low-Level Analysis. To detect the presence of an edge in an image, operators such as the Sobel operator, the Marr-Hildreth operator, and a variety of first and second derivatives of Gaussians are utilized.
- Feature Analysis further involves two approaches namely, the Sequential Feature Searching and the Constellation Analysis. Sequential Feature Searching depends upon the relative positioning of the individual facial attributes while Constellation Analysis detects features from complex backgrounds in multiple poses.
- Finally, the Active-Shape Model is divided into Deformable Templates, Snakes and Smart Snakes. A head boundary is created by Snakes that latch on to the nearby edges to create initial contours. As an extension of the Snakes model, Deformable Templates use the global information of the eye to extract facial features. Smart Snakes are also known as Point Distributed Models or PDMs that produce parameterized shapes derived from pure statistics.
Image-based
- The image-based approach uses Neural Networks, Linear Subspace methods, and statistical approaches.
- In the Linear Subspace method, detection depends upon Factor Analysis, Linear Discriminate Analysis, and Principal Component Analysis.
- Face knowledge is incorporated into the Neural Network architecture with specific window sizes meant to capture optimal facial information.
- Based on information theory, the statistical approach involves a measurement between two probability density functions.
Advantages of the Facial recognition software
As part of an authentication strategy, FRT holds some of the biggest advantages and FRS, as an agile tool comes with some of the best benefits for different users encased within diverse areas. FRS is now being experimented by military, intelligence, law enforcement, and even humanitarian services while corporations have realized its benefits in many ways.
Safety and law enforcement
Definitely, FRS sees its biggest and most compelling argument within law enforcement. With an aim to inculcate efficacy, FRS can identify ‘wanted’ criminals, easily and can, additionally, help law enforcement officers on patrol duty in heavily populated areas, to detect criminals or other misgivings.
Intelligence
Another undeniably challenging area where FRS does seem to affirm itself is right here. Intelligence agencies can use sophisticated facial recognition to exploit billions of images splashed across social media, video conferences and emails. Obviously, there is a need for FRS to aid governments to find intelligence targets across the globe.
Enterprises
Today, commercial enterprises and companies are employing FRS either for convenience, internal security or for marketable purposes. There are several other uses for FRS as well, such as identifying customer preferences based on their items of choice and the path that they take in a store. This data is run through smart analytics that monitors footsteps, predilections and even customer experience.
Healthcare
Achieve contactless information about a target to obtain sensitive medical information. Other biometric solutions potentially require the target to stay in contact with the system. But FRS takes it a step further where facial recognition can also be used for genetic screening while facilitating easy identity management. Besides, medical records can be fetched quickly and insurance companies can authorize transactions in a matter of minutes.
Other areas where XCEL Corp facilitates constructive usage of FRS is in marketing and product portfolio management, financial services that involve authentication systems and much more. Biometrics and facial recognition are a new wave of validation solutions. To turn guesses of a facial recognition program into learned modifications, XCEL Corp incorporates a number of different algorithms.
Today’s advanced facial recognition in the 21st century comes along with deep learning.



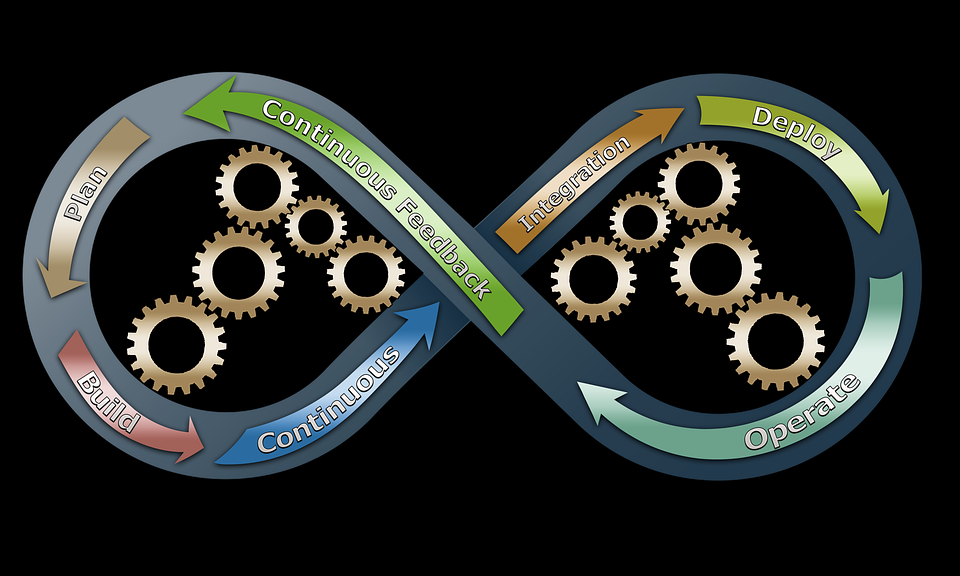 DevOps, as the name suggests, essentially combines development and information technology operations, to save on costs and duration of development. High-quality software is delivered…
DevOps, as the name suggests, essentially combines development and information technology operations, to save on costs and duration of development. High-quality software is delivered…